LDAP
Neben der internen Benutzerverwaltung besteht die Möglichkeit, Benutzerinformationen (Stammdaten + Authentifizierung) über LDAP (MS Active Directory) zu beziehen. Diese Option wird in den Mandanteinstellungen im Bereich "Anmeldeeinstellungen für Benutzer" aktiviert und steht nur bei der Verwendung einer entsprechendne Lizenz zur Verfügung. Ferner muss der anzubindende Server LDAP-Objekte vom Typ "user" mit mindestens dem Attribut "UserPrincipalName" zurückliefern. Im Gegensatz zu internen Benutzern, können bei LDAP-Benutzern die Stammdaten und das Passwort nicht geändert werden. Dies erfolgt weiterhin über die entsprechende Standardanwendung.
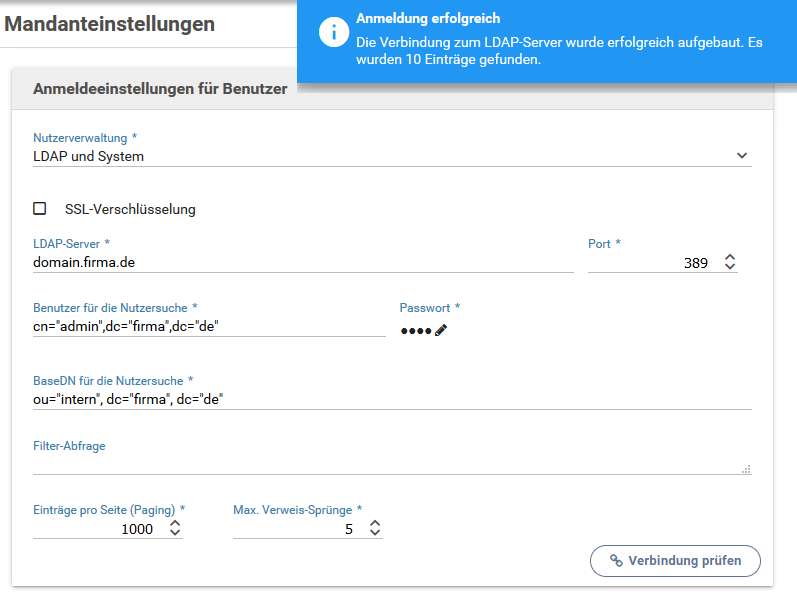
Konfiguration des LDAP-Servers am Mandanten
Im Abschnitt Anmeldeeinstellungen für Benutzer innerhalb der Mandanteinstellungen muss für das Verwalten von Benutzern aus einem LDAP-System die Nutzerverwaltung auf nur LDAP oder LDAP und System geändert werden. Anschließend ist die Verbindung zum LDAP-Server konfigurierbar:
- SSL-Verschlüsselung: Gibt an, ob der Transport mit dem LDAP-Server mittels SSL verschlüsselt durchgeführt werden kann/soll.
- LDAP-Server: Name oder IP Adresse des LDAP-Servers
- Port: Kommunikationsport des LDAP-Server
- Benutzer für die Nutzersuche: Dieser Account muss das Recht haben, Suchanfragen (Benutzerobjekt) an den LDAP-Server zu senden. Siehe auch Benutzer anlegen.
- Passwort: Passwort des Benutzers für den Login am LDAP-Server.
- BaseDN für Nutzersuche: BaseDN unter der die zu authentifizierenden Benutzer gesucht werden. Beispiel: ou="intern", dc="firma", dc="de"
- Filter-Abfrage: Optionaler LDAP-Filter, um innerhalb der Menge der Benutzer-Objekte weitere Einschränkungen anzuwenden (Tutorial)
- Einträge pro Seite (Paging): Gibt an, wie viele Eintrage vom LDAP-Server pro Seite erwartet werden. Ein Wert von 0 deaktiviert dies und es werden vom Server alle Werte erwartet
- Max. Verweis-Sprünge: Gibt die maximale Anzahl von durchzuführenden Verweis-Sprüngen (Referral-Hops) auf dem LDAP-Server an. Bei einem Wert von 0 wird das Folgen von Verweisen deaktiviert
Installation von Zertifikaten im Java-TrustStore
Das für die Ausführung des Application Containers verwendete Java muss dem Zertifikat des LDAP-Servers vertrauen.
Hierzu kann es nötig sein, das Root-Zertifikat, mit dem das Zertifikat des LDAP-Servers ausgestellt wurde, in den Java-Truststore zu importieren. Eine Anleitung dazu befindet sich auf der Seite Zertifikate in Keystores importieren.
Verbindungsprüfung
Bereits vor dem Speichern besteht die Möglichkeit, die eingegebenen Daten zu testen. Die Schaltfläche "Verbindung prüfen" testet hierbei, ob eine Verbindung zum LDAP-Server erfolgreich aufgebaut werden kann. In der Erfolgsmeldung wird die Anzahl der gefundenen Benutzerobjekte zurückgegeben.