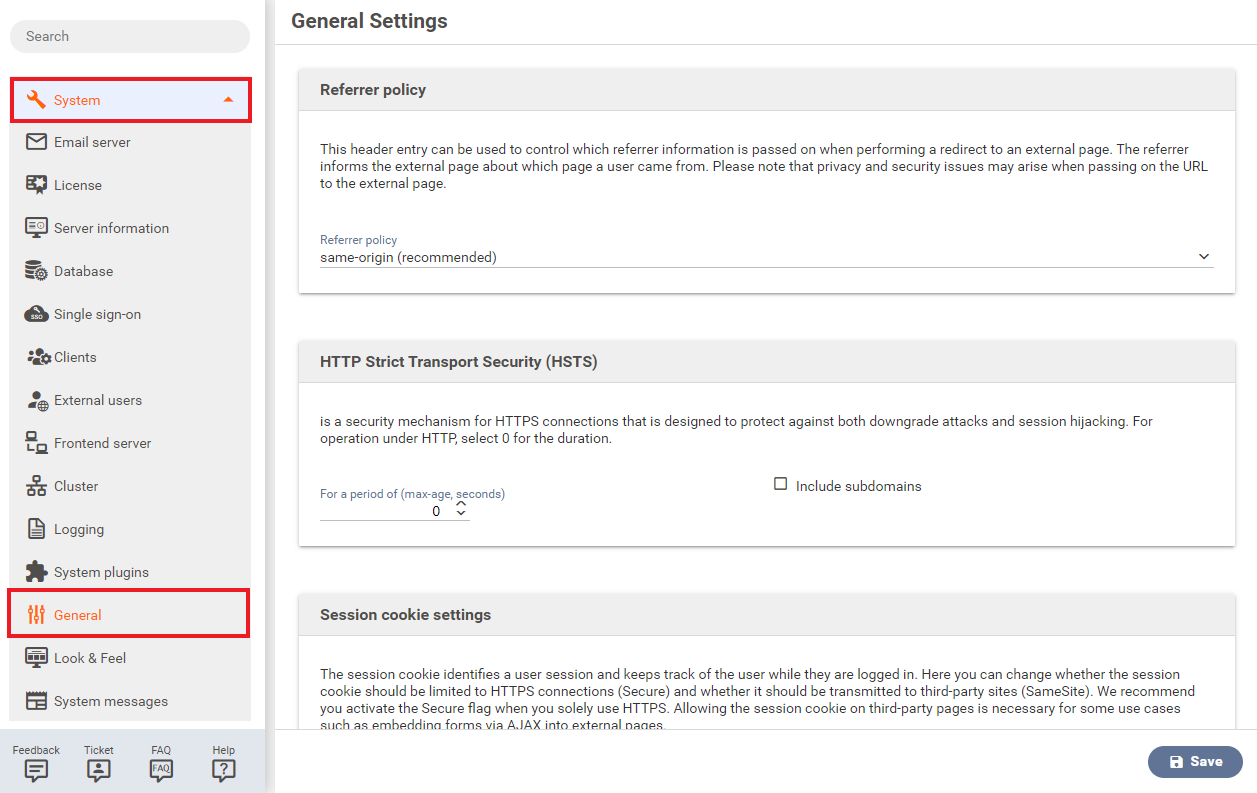
General
The menu General allows the configuration of general FORMCYCLE settings like cache configurations or upload limits.
Security
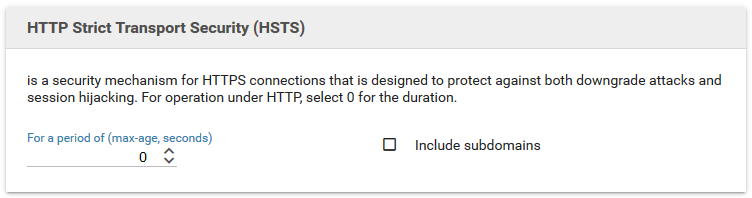
HTTP Strict Transport Security (HSTS)
HTTP Strict Transport Security (HSTS) is a security mechanism for HTTPS connections that prevents the connection encryption from being disabled by downgrade attacks, and also guards against session hijacking. If you need to support HTTP, enter 0 as the value.
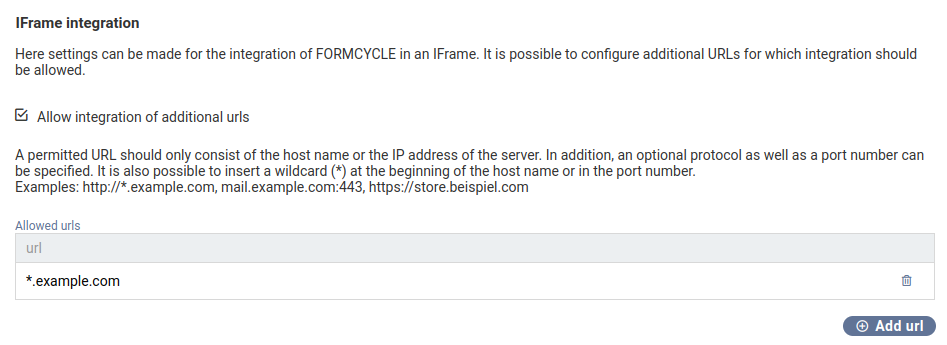
Iframe integration
By default, Xima® Formcycle blocks any attempts by third-party pages to include backend pages as iframes due to security concerns. In case it becomes necessary to include backend pages as an iframe, you can whitelist allowed third-party pages in this menu. The values you enter here are used for the frame-ancestors directive of the Content-Security-Policy HTTP header, see for example mdn web docs for an in-depth descrption of the allowed values.
Password policies
The strength of all user passwords can be configured here. Passwords may not be shorter than a minimum length of 8 characters, but a higher minimum length can be configured. Different character sets (like letters in general, lowercase letters, uppercase letters, digits or special characters) can be forced to be contained in all passwords. After setting password policies, all new and all changed passwords must follow these. Existing passwords will not be changed, even if they do not conform the new password policies.
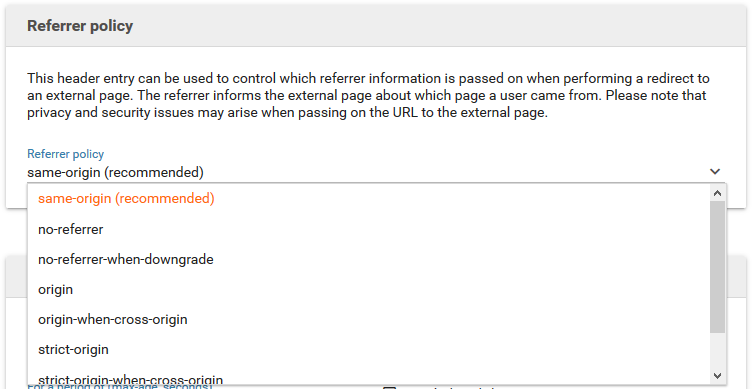
Referrer policy
This header entry can be used to control which referrer information is passed on when performing a redirect to an external page. The referrer informs the external page about which page a user came from. Please note that privacy and security issues may arise when passing on the URL to the external page.
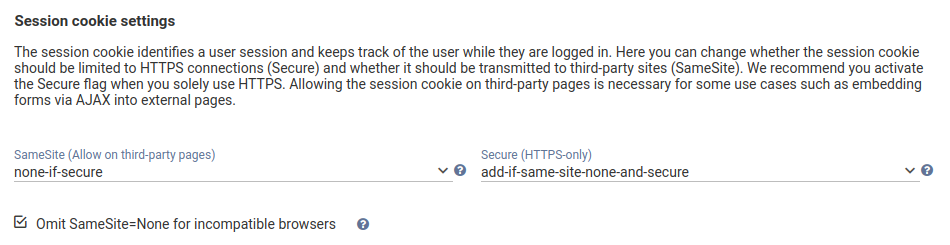
Session cookie settings
The session cookie identifies a user session and keeps track of the user while they are logged in. Here you can change whether the session cookie should be limited to HTTPS connections (Secure) and whether it should be transmitted to third-party sites (SameSite). We recommend you activate the Secure flag when you solely use HTTPS. Allowing the session cookie on third-party pages is necessary for some use cases such as embedding forms via AJAX into external pages.
Content-Security-Policy
7.2.1+ Lets you add additional policies to the Content-Security-Policy header. Different values can be stored for backend (administration interface, designer, inbox) and for frontend (web forms).
Content Security Policy (CSP) is an added layer of security that helps to detect and mitigate certain types of attacks, including Cross-Site Scripting (XSS) and data injection attacks. These attacks are used for everything from data theft, to site defacement, to malware distribution. A primary goal of CSP is to mitigate and report XSS attacks. CSP makes it possible for server administrators to reduce or eliminate the vectors by which XSS can occur by specifying the domains that the browser should consider to be valid sources of executable scripts.
For a list of available policies, see e.g. this Mozilla page.
Protocol
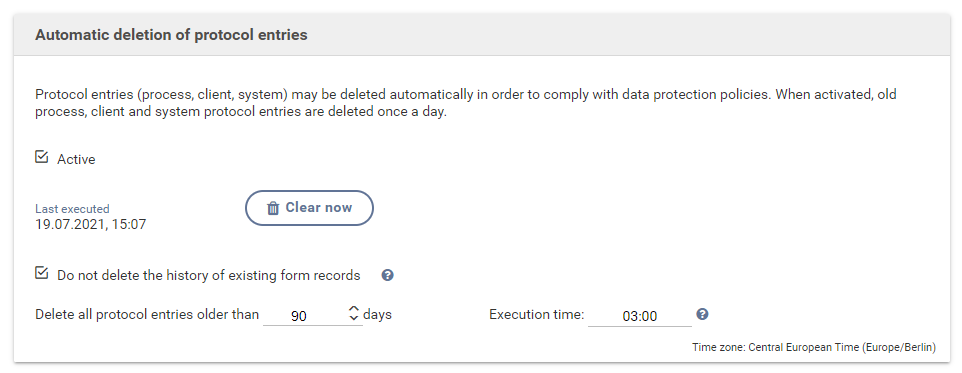
Automatic deletion of protocol entries
Protocol entries (from processes, clients, system) that are outdated can be deleted automatically. At a specified time of the day all protocol entries are deleted that are older than the specified number of days. By using the "clear now" button all protocol entries can also be deleted instantly. After the automatic deletion of protocol entries, a new protocol entry is created containing information about the amount of automatically deleted protocol entries.
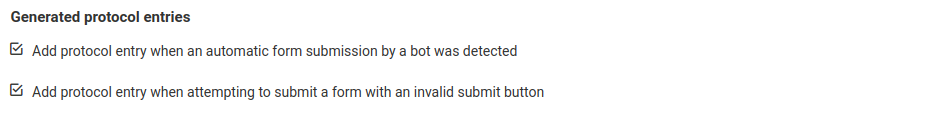
Generated protocol entries
- Add protocol entry when an automatic form submission by a bot was detected
- Xima® Formcycle tries to detect attempts by machines (bots) to submit forms automatically. When a bot was detected, the submission is blocked. If this option is enabled, a processing protocol entry is created.
- Add protocol entry when attempting to submit a form with an invalid submit button
- You can add buttons to a form that allows users to submit the form. Within the workflow, you can check whether a certain buttons was pressed and run certain actions depending on which button was pressed. Starting with version 7, it is possible to validate whether the submit button actually existed in the form, which helps prevent form records from being manipulated. If this option is enabled, a processing protocol entry is created when a form was submitted with an invalid submit button.
Limits
Form and file cache
The file cache stores files used by the system, the form cache stores rendered HTML forms.
| Property | Default value | Explanation |
|---|---|---|
| Max disk size | -1 | Maximum size in MB of what the form cache stores in the file system. No limit when set to -1. If set to 0, the file system is not used by the cache. |
| Max Heap size | 75 | Maximum size in MB of what the form cache stores in-memory. If set to 0, the in-memory form cache is disabled. |
| Time to idle | 0 | Time interval in seconds until an item in the form cache is removed when it is never accessed during that time interval. Set to 0 to disable. |
| Property | Default value | Explanation |
|---|---|---|
| Max disk size | -1 | Maximum size in MB of what the file cache stores in the file system. No limit when set to -1. If set to 0, the file system is not used by the cache. |
| Max heap size | 75 | Maximum size in MB of what the file cache stores in-memory. If set to 0, the in-memory file cache is disabled. |
| Time to idle | 0 | Time interval in seconds until an item in the form cache is removed when it is never accessed during that time interval. Set to 0 to disable. |
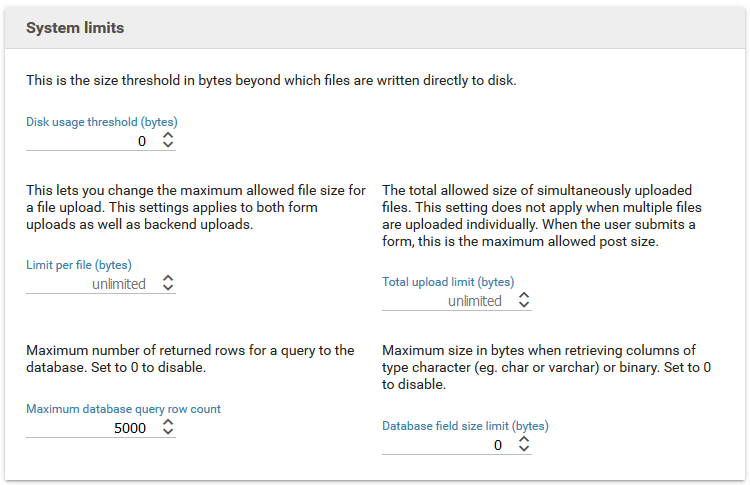
System limits
| Property | Default value | Explanation |
|---|---|---|
| Disk usage threshold | 0 | This is the size threshold in bytes beyond which files are written directly to disk. |
| Limit per file | Maximum size in bytes for file uploads within forms. Applies to each file individually. Set to -1 or no value to disable. This settings applies to both form uploads as well as backend uploads. | |
| Total upload limit | The total allowed size of simultaneously uploaded files. This setting does not apply when multiple files are uploaded individually. When the user submits a form, this is the maximum allowed post size. Set to -1 or no value to disable. | |
| Maximum database query row count | 5000 | Maximum number of returned rows for a query to the database. Set to 0 to disable. |
| database field size limit | 0 | Maximum size in bytes when retrieving columns of type character (eg. char or varchar) or binary. Set to 0 to disable. |
Configuration
Loopback URL
Some features (such as form preview images or PDF print) require the server to open a form. In cluster configurations or environments in which the internal and external domains are different, this parameter is used to configure the internal availability (e.g. http://localhost:8080/formcycle).
License
- Allow automatic license update through external notifications
- When this option is enabled, one can trigger a license update via an HTTP request to http://example.com/formcycle/license/notify?key=LICENSE_KEY, where http://example.com/formcycle should be replaced with the actual URL of the Xima® Formcycle server and LICENSE_KEY should be replaced with the license key of the license to update.